Top Rated Avast Security Software:
Top Rated AVG Security Software:
Your best source for Avast and AVG Antivirus & Total Security Software:
www.softzaar.com digital software store is the best and most safe source to buy genuine Avast and AVG Antivirus Security Software in India.
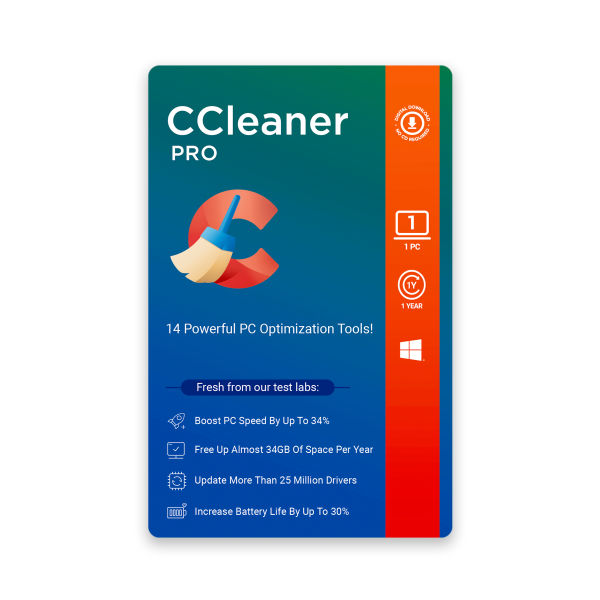
Get the latest PC/Mac/Laptop/Mobile - Protection, Privacy and Performance enhancing Avast, AVG, CCleaner, HMA VPN software such as;
Avast Ultimate Multi-Device, Avast Ultimate PC Suite, Avast Premium Security, Avast SecureLine VPN, Avast Cleanup Premium, AVG Ultimate Multi-Device, AVG Internet Security, AVG PC TuneUp, CCleaner, CCleaner Professional, at the best prices anywhere in the world.
Get the best mobile device protection through: Avast Mobile Security Ultimate with VPN and AVG Antivirus for Android – Pro.
Avast, AVG and CCleaner security products are available through email delivered digital key - within 2 hours of order placement, complimented by a wide range of digital payment options.